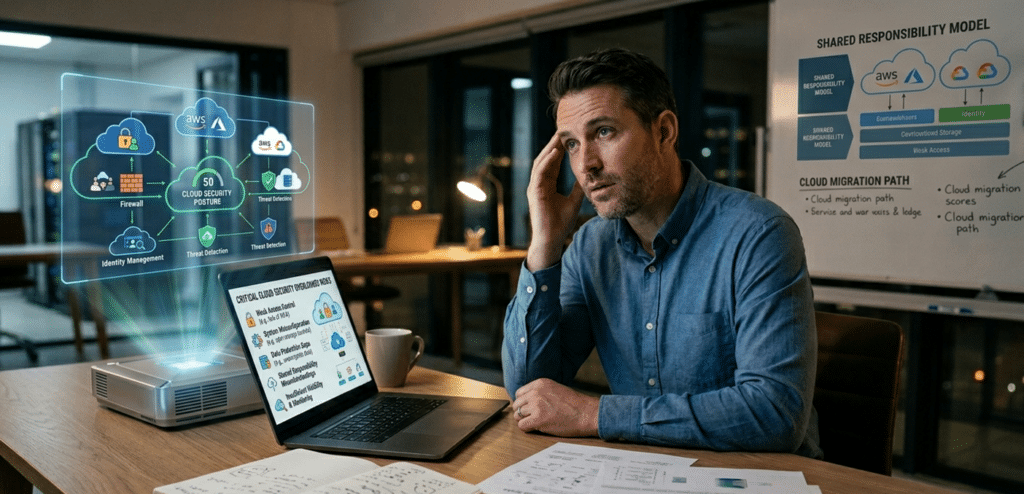
Cloud platforms offer flexibility and scalability, but they also introduce security risks that are often misunderstood or overlooked. Many IT managers assume their cloud provider handles all aspects of security, which can leave critical gaps in areas such as access control, system configuration, and data protection.
In this article, we break down the most common cloud security risks organizations overlook and why they remain a challenge in today’s fast-moving digital environments. We’ll also share practical steps you can take to strengthen your defences, reduce exposure, and improve resilience.
If your organization relies on the cloud, understanding these hidden vulnerabilities is essential for stronger security and compliance.
The Shared Responsibility Model: Clarifying the Divide
- Physical data centers
- Hardware and networking infrastructure
- Core platform services
- Global availability and redundancy
Customer responsibilities include:
- Data classification and protection
- Identity and access management (IAM)
- Application and configuration security
- Permissions, policies, and governance
- Compliance requirements
Many SMBs misunderstand this split, believing the cloud is fully managed and secure by default. In reality, the vast majority of breaches stem from customer-side issues, such as misconfigurations or weak controls, rather than provider failures.
1. Misconfigured Cloud Storage and Services
Cloud environments are flexible, which makes them easy to deploy, but also easy to misconfigure. A single oversight can expose sensitive data to the public internet within hours.
Common cloud misconfigurations include:
- Storage buckets left publicly accessible
- Databases without proper authentication
- Overly permissive user or service permissions
- Default security settings left unchanged
- Weak firewall or network access rules
These issues are often caused by human error during rapid deployments or updates and are a leading contributor to cloud incidents, with studies estimating that misconfigurations account for 23–38% of breaches. Automated scanners can quickly detect exposed resources, increasing the risk of data theft or ransomware.
The main challenge is visibility, these issues often go unnoticed until after they are exploited.
To reduce risk, implement automated configuration scanning, enforce infrastructure-as-code with policy controls, and continuously audit cloud resources. Partnering with experienced managed hosting services providers can help maintain proper configurations.
2. Weak Identity and Access Management (IAM)
In cloud environments, identity has become the new perimeter. Once attackers obtain valid credentials, traditional network defences offer little protection, and lateral movement becomes effortless.
Frequent IAM shortcomings include:
- Excessive "admin" privileges for everyday users
- Shared credentials across teams
- Absence of role-based access control (RBAC)
- Missing or inconsistently enforced multi-factor authentication (MFA)
- Ineffective offboarding of former employees or contractors
Over time, users accumulate unnecessary permissions, creating “privilege sprawl” that dramatically expands risk. A single compromised account can then expose critical systems, customer data, or financial records. Best practices involve enforcing least-privilege principles, enabling MFA universally, implementing just-in-time access where possible, and performing regular access reviews to revoke unnecessary rights before they become liabilities. Managed IT services teams often assist with these IAM disciplines.
3. Lack of Visibility Across Cloud Environments
SMBs frequently use multiple clouds, SaaS tools, and third-party integrations to boost productivity. This diversity, however, fragments security oversight and creates blind spots that attackers readily exploit.
Without centralized visibility, teams struggle with:
- Shadow IT (unauthorized tools and services)
- Inconsistent policies across platforms
- Limited monitoring of user activity and data flows
- Delayed threat detection
- Challenges in tracking sensitive data movement
Many IT teams only discover issues after an incident, when missing logs slow response and recovery. A unified monitoring system that consolidates logs and alerts enables faster detection and more effective incident response.
4. Inadequate Backup and Disaster Recovery
A common misconception is that cloud providers fully protect data from loss. While they offer infrastructure redundancy, they do not cover customer-side risks such as accidental deletion, ransomware, application errors, insider threats, or replication failures.
Without a robust backup strategy, data loss can be permanent and recovery costly. Effective plans define:
- Recovery Time Objective (RTO): Maximum acceptable downtime
- Recovery Point Objective (RPO): Tolerable data loss
- Backup frequency, testing, and retention schedules
- Immutable or off-site backups for ransomware resilience
Regular testing ensures backups are reliable and truly recoverable. Treating backup and recovery as a core security control, not an afterthought, minimizes disruption and supports business continuity even in the face of sophisticated attacks. For practical guidance, review resources like TechMasters’ guide to SMB data backup strategies.
5. Poor API and Integration Security
APIs power modern cloud workflows, connecting services, automating processes, and linking SaaS applications. Yet they dramatically expand the attack surface, often serving as the unseen gateway for breaches.
Typical risks include:
- Unauthenticated or exposed endpoints
- Hardcoded or unmanaged API keys
- Unencrypted data transmissions
- Overly broad permissions for integrations
- Outdated or unvetted third-party connectors
As integrations multiply with business growth, so do entry points for attackers. Regular audits, key rotation, rate limiting, and least-privilege integration policies are critical to governing this expanding surface and preventing cascading compromises. Experienced providers of managed hosting services can help secure these integrations.
6. Compliance and Data Residency Gaps (Especially for Canadian Businesses)
For organizations in Canada, compliance is a legal imperative, not optional. Laws like the Personal Information Protection and Electronic Documents Act (PIPEDA) mandate responsible handling of personal information, including appropriate safeguards, consent, and accountability.
Many businesses lack clear visibility into:
- Physical data storage locations
- Cross-border data transfers
- Retention periods
- Access controls and audit trails
These risks are particularly high in regulated industries like healthcare, finance, and legal services, where breaches can lead to fines, legal action, and reputational damage. Strong data protection, along with encryption and residency controls, helps support compliance and build trust. Canadian-focused IT partners often address PIPEDA-aligned cloud choices.
7. Overconfidence in Cloud Provider Security
A common mindset trap is assuming “the provider handles everything.” While providers secure the foundation, they do not manage your accounts, permissions, configurations, or internal policies.
This overconfidence breeds complacency, delaying basic hygiene like patching, reviews, and monitoring that are essential for real protection. Security in the cloud demands active, ongoing management, not passive reliance, if organizations hope to stay ahead of evolving threats. Professional cybersecurity support through managed services helps close this gap.

Strengthening Your Cloud Security Strategy
Effective cloud security relies on consistency rather than complexity. Prioritize these foundational steps:
- Apply least-privilege access everywhere
- Mandate MFA for all users and service accounts
- Conduct continuous configuration and permission audits
- Deploy real-time monitoring and centralized logging
- Use Cloud Security Posture Management (CSPM) tools to catch drift
- Maintain tested, versioned, and immutable backups
- Regularly review and secure third-party integrations and APIs
For resource-constrained SMBs, partnering with a managed IT services provider can deliver expert oversight without straining internal teams. Adopting zero-trust principles and automating where possible further reduces human-error risks that continue to drive the majority of incidents.
The Risks You Don’t See Are the Most Costly
Most cloud breaches result not from advanced attacks, but from overlooked basics: misconfigurations, weak IAM, poor visibility, and untested backups. The real challenge isn’t adopting cloud technology, it’s securing it properly once it’s in use, especially as environments grow more complex.
The encouraging news? These risks are largely preventable through disciplined practices. By embedding governance, monitoring, regular audits, and compliance discipline into operations, organizations can dramatically lower their exposure while gaining confidence in their cloud investments.
Identifying hidden vulnerabilities early prevents expensive incidents later and turns security into a genuine business enabler. Ultimately, strong security delivers more than protection, it ensures continuity, builds customer trust, and supports long-term resilience in a digital-first economy.
Reach out to a trusted Canadian managed IT services company for a no-obligation consultation.
Frequently Asked Questions About Cloud Security
What are the biggest cloud security risks for SMBs?
Misconfigured storage, weak identity controls, insufficient monitoring, inadequate backups, and poor access management top the list. These are especially prevalent when cloud adoption outpaces formal security governance, leaving smaller teams overwhelmed by complexity.
What are common cloud security mistakes businesses make?
Assuming the cloud is secure by default, skipping MFA, neglecting permission reviews, and prioritizing speed over configuration audits. Teams often focus on deployment velocity at the expense of sustained security, which compounds risks over time.
What are cloud misconfigurations?
Incorrect settings such as public storage access or overly permissive roles that unintentionally expose systems or data. They commonly arise during initial setup, updates, or scaling and can persist undetected until exploited.
What is the shared responsibility model in cloud security?
It clearly divides duties: providers secure the infrastructure (“of the cloud”), while customers secure their data, identities, applications, and configurations (“in the cloud”). Most breaches trace back to gaps in the customer’s portion, highlighting why education on this model must be a priority for every IT team.
How can SMBs improve cloud security quickly?
Begin with universal MFA, least-privilege access, regular configuration audits, and centralized monitoring. These steps deliver rapid risk reduction before layering on advanced tools. Even modest investments in these basics can significantly lower breach likelihood.
Why is cloud compliance important in Canada?
It ensures adherence to requirements like PIPEDA, safeguarding personal information and minimizing legal, financial, and reputational risks. Responsible practices also enhance customer confidence in how data is handled.